Part 2. The first post showed what the technique produces. This post covers what it costs to produce, and what those numbers should change about how you fund your OT cybersecurity program.
Earlier this week I said AI was closing the knowledge gap for attackers faster than the industry was ready for. This is the technique, demonstrated.
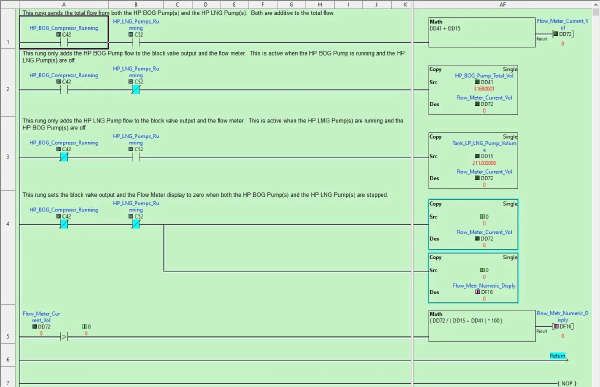
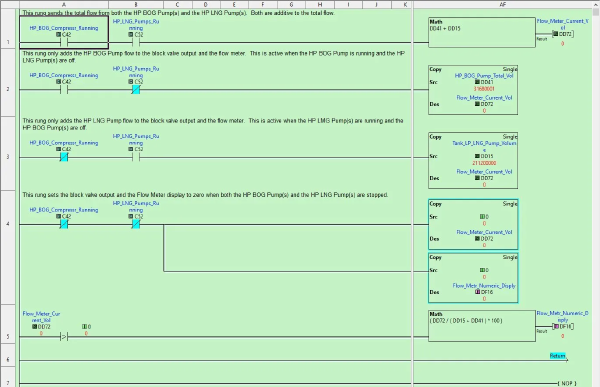
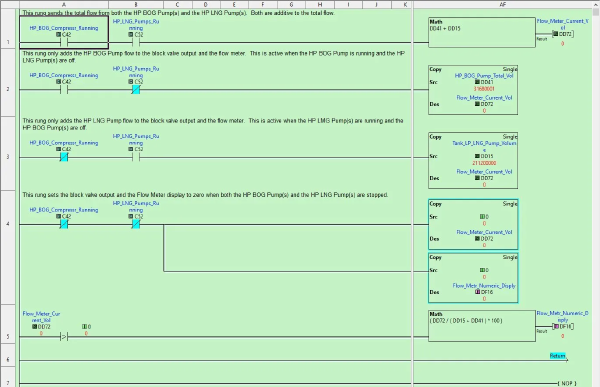
TL;DR for OT leadership: Threat actors no longer need years of industrial experience to plan targeted attacks on your operational process. They need your configuration files (logic exports, address maps, HMI project files, manufacturer reference documents) and access to a production AI tool. With those, the AI tool supplies the process expertise the attacker does not have. It reads the logic, infers the physics, maps cross-system dependencies, and produces ranked attack paths with protocol-level instructions for executing them. The industrial-process knowledge gap that used to be a natural barrier against precision attacks has collapsed. For leadership, that changes three priorities. First, configuration files are process intelligence and must be protected like safety documentation. That means backup validation, integrity checks, and inventories of every copy wherever it lives, including copies held by vendors and contractors, and copies on the IT network. Second, remote access to engineering workstations deserves the same scrutiny you apply to your highest-value production systems, because that is where the intelligence lives. Third, the investment required for an adversary to weaponize this technique is trivial. A single analyst workday and a few dollars of API cost. Assume it is in use today, and fund your teams accordingly.
It’s not that attackers got smarter. It’s that the tools available to them are closing the knowledge gap at a pace nobody anticipated. That changes things.
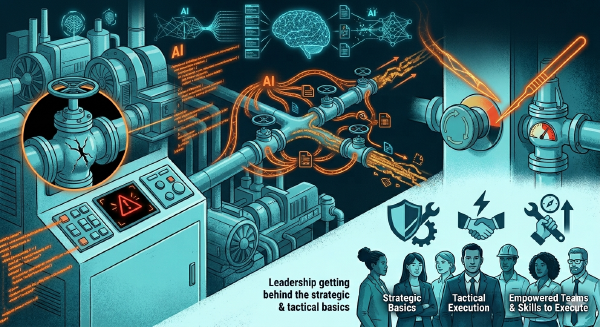
TL;DR: AI is accelerating ICS/OT threats in three big ways. Deployed OT solutions will always have some type of vulnerability, it is the nature of this industry. Tools like Mythos can chain vulnerabilities while also manipulating physical process data and the automation pipelines built on top of it. And attackers who previously lacked the domain knowledge to cause precision damage can now get it on demand. Not just shut systems off, but surgically target operational systems. The answer isn’t a new cybersecurity framework. It’s leadership getting behind the strategic and tactical basics, empowering their teams, and making sure those teams have the skills to execute.
TL;DR # Setting up a proper Windows testing environment for ICS/OT security tool development goes beyond spinning up a single VM. You need multiple Windows versions, from legacy Windows 7 through Server 2022, templated, sysprepped, and network-isolated so you can rapidly deploy clean test systems and tear them down when you’re done. This post summarizes my experience building a Proxmox-based development lab with automated VM management for testing Sysmon configurations and security scripts across every supported Windows version. The complete setup guide is available as a PDF download. We document these projects to both remember what we have done and also help others with similar projects.
This morning I was thinking about completing an article I was writing about KPIs and OKRs. The more I wrote, the more I realized I was just regurgitating research and making pity comments. Which means, it was crap. So, I refocused and turned to AI to help me. I ask Google’s Gemini the following question.
This last week was the week of Battery Energy Storage System (BESS). Joe Weiss released a blog post titled Cyber-vulnerable battery systems are catching fire and communicate directly to China where he discusses his concerns about threat actors from the People Republic of China (PRC) remotely accessing BESS deployments in the United States. While I share the concern I am not a fan of “reading between the lines” to correlate an event with threat actor activities.
The US Treasury Department is an industrial control environment integrated with an active business environment. This organization collects taxes, pays bills for the United States, produces coins and currency (ICS controllers, field devices, servers, and applications), manages government accounts, and enforces tax and finance laws. The recent access to access that has been provided to the Department of Government Efficiency (DOGE) team equates unmoderated administrative access to this control environment. The US Treasure Department one piece of the United States’ critical infrastructure.
Today I had to remind myself to tell a team leader about an IT cybersecurity team member that provides superior security assessment work for a utility client. The IACS and OT industry likes to say that IT administrators and cybersecurity professionals cannot provide good guidance or do active assessments safely in production environments. This individual’s contributions to the vulnerability assessment of complex production and test environments continues to be invaluable and has helped to improve the design and deployment of solutions affecting millions of people supported by the utility.
In his recent article, titled Critical infrastructures cannot be secured because network security and engineering won’t work together, Joe Weiss has provided the IACS cybersecurity industry with an example of hyperbole and fear mongering what needs to be stamped out rather than perpetuated. The advancement and maturity of this field will not evolve effectively when build on, or supported by, this biased and bigoted vernacular. It is difficult to call out all the issues in his meandering post. So, I will focus on three important topics where he needs to take a hard look at his beliefs and the approach he is bringing to the security and safety of industrial and automation control environments.
Originally posted at Claroty NexusConnect on May 9, 2024
The Cybersecurity Safety Challenge # I started thinking about the safety issues for security assessments when I was asked to attend a conference for amusement rides and parks. Safety has always been paramount in this industry and their teams are working hard to understand and improve how cybersecurity fits into the phases of a ride’s lifecycle.
Recently, I have noticed people emphasizing the name of certifications and personally attacking the people who obtain them. This is unfortunate as it is shining light on the wrong subject. The value of a certification is not in the name. The value of the certification is that it is an indication that an individual has received a level of instruction and demonstrated the ability to retain, reference, and recall that information. It is this foundation of knowledge that the individual can be held accountable for using during decision making.
In February 2023 I was attending a conference for safety. I was introduced to many new people with roles that involved safe implementation of processes, equipment, and manual procedures that support the entertainment and safety of people all around the world. During one of my conversations, I was told that people purchasing services from large industrial control and automation vendors are not asking for people that have achieved the GIAC GICSP certification. They are specifically asking for people that have achieved the ISA/IEC 62443 Cybersecurity certifications. That was the moment I decided I was going to achieve the ISA/IEC 62443 Cybersecurity Expert certification before the end of 2023.