It’s not that attackers got smarter. It’s that the tools available to them are closing the knowledge gap at a pace nobody anticipated. That changes things.
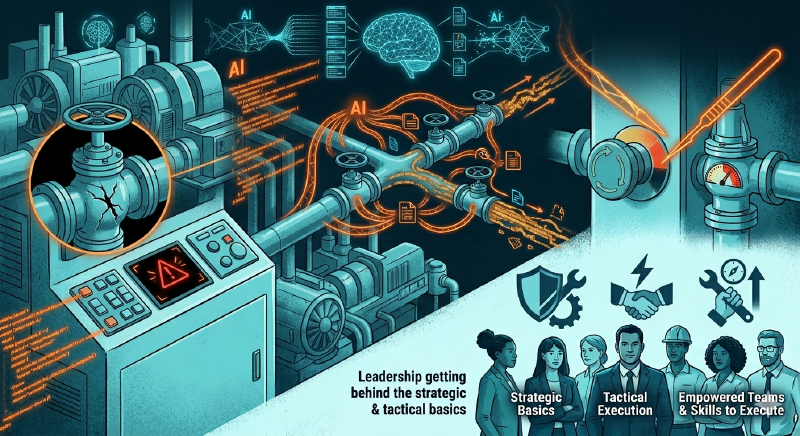
TL;DR: AI is accelerating ICS/OT threats in three big ways. Deployed OT solutions will always have some type of vulnerability, it is the nature of this industry. Tools like Mythos can chain vulnerabilities while also manipulating physical process data and the automation pipelines built on top of it. And attackers who previously lacked the domain knowledge to cause precision damage can now get it on demand. Not just shut systems off, but surgically target operational systems. The answer isn’t a new cybersecurity framework. It’s leadership getting behind the strategic and tactical basics, empowering their teams, and making sure those teams have the skills to execute.
OT vendors are in a tough spot#
OT vendors are dealing with the same reality as every other technology vendor right now. Vulnerabilities are going to be found in their products, and they’re going to be found faster. The difference is that OT systems were designed under an assumption of isolation. The thinking was that surrounding countermeasures would carry the load because the systems themselves were never hardened for an exposed environment. In many cases that assumption is still being tested, and the results aren’t great.
The EU Cyber Resilience Act is going to be one of the bigger forcing functions on the vendor side, at least for those serving European clients. It puts real requirements behind what has largely been voluntary. For everyone else, the pressure is building from a different direction: the incidents themselves.
The workflow is the attack surface#
I’ve always said that the telemetry workflow is one of my biggest concerns in OT security, and AI tools are making that concern a lot more concrete. The workflow isn’t complicated to describe. Data is generated at the process level. It moves from sensors to controllers to applications to databases, and from there it gets analyzed, stored, distributed, and acted on. Every handoff in that chain is a potential point of manipulation.
Most offensive security thinking focuses on systems and applications. That’s where the vulnerabilities live, so that’s where the attention goes. But in an industrial environment you have to add physics computations at the process level to that picture. The integrity and availability of the data those computations produce, and where that data ends up being used, is a huge gap in how most people think about OT attacks.
A tool like Mythos, covered recently by VentureBeat, illustrates exactly this. It chains vulnerabilities to achieve objectives in ways that go beyond moving laterally through systems. With enough information, through security breaches or (worse) authenticated unauthorized access, the attack can, but does not have to, target the physical process layer, it can target the data flowing in and out of it. That’s a meaningful shift.
The knowledge gap just got a lot smaller#
Here’s what concerns me most, and I say this as a security researcher, OT penetration tester, and an OT cybersecurity instructor. Take a compromised OT environment where an attacker has pulled configuration files, has access to the vendor management software, and can see how the process is set up. That used to require real domain expertise to exploit with any precision. You had to understand the process, the controller logic, the safety system design. That knowledge took years to develop.
Now feed that same material into a capable AI model. It will reconstruct the process logic, explain the math the controller is managing, map the dependencies, and tell you what conditions trigger which events. Then ask it how to disrupt the process. It will tell you that too.
This isn’t theoretical. I will be running a workshop, at the SANS ICS Summit 2026, that puts students through exactly this scenario using ladder logic screenshots and extracted configuration data. The AI explains the process. It identifies what to target. It works, and it works with current production models and does not require Mythos. What was a nation-state capability a decade ago is becoming accessible to a much wider range of threat actors, not because those actors developed new skills, but because the tools arrived before the industry was ready for them.
The industry is also creating new risks for itself#
Separate from what attackers are doing, there’s a risk the industry is building on its own. Electrical vendors and others are actively integrating AI to reduce or remove humans from operational decision loops. The pitch is faster response and lower operator burden. The problem is that AI-driven automation running on manipulated telemetry, or operating outside what its designers anticipated, can cause consequences that move faster than anyone can intervene. This isn’t hypothetical. Vendors are shipping this direction right now, and the cybersecurity implications are not keeping pace with the deployment timelines. That’s a serious problem that I know SANS ICS leadership is monitoring closely.
Get back to basics, and get your teams ready#
Preparing for this DOES NOT require a new cybersecurity framework (at least you don’t have time to wait for one). The SANS ICS Cyber Kill Chain and the SANS 5 Critical Controls are still the right foundation. These approaches exist because ICS/OT environments have consequences that generic cybersecurity frameworks don’t account for, and they give organizations a clear structure for protecting operations, detecting adversary activity, responding before the physical process is impacted, and recovering cleanly when it is. SANS ICS leadership has been driving this approach for years, and in a moment where the noise level is high, that clarity matters.
What the current environment demands is that organizational leadership, not just security teams, actively champions this work. Your teams likely already know where the gaps are. They need backing, prioritization, and the resources to act. In a landscape that’s shifting this fast, getting the basics executed well is more valuable than chasing whatever is new.
Assessment is where you find out how exposed you actually are. SANS ICS613 ICS/OT Penetration Testing and Assessments course is built for exactly this moment. The course takes a top-down penetration testing approach while building a bottom-up understanding of operational impact, so the output isn’t a generic vulnerability list but a clear picture of which attack vectors carry the most consequence for your operations. It moves from passive to active, starting with bench testing and protocol analysis before moving into active penetration testing. Remote Access gets significant attention, and it should. It’s one of the 5 Critical Controls for a reason, it’s consistently exploited, and the gap between what organizations think their remote access posture is and what it actually is tends to be significant.
A note for leadership
Your security teams are your best asset right now. The tools available to threat actors are advancing faster than most organizations expected, and your people closest to the systems are the ones who can do something about it.
Back them up. Make sure they have current training. And treat ICS/OT cybersecurity as an operational issue, because that’s exactly what it is.
For teams with limited OT monitoring coverage, tools like ICS Watch Dog offer a practical way to improve visibility quickly and without significant cost, especially in environments where broader security tooling hasn’t landed yet. SANS ICS leadership is also developing a dedicated SOC curriculum for industrial environments. More on that when it’s ready.
The fundamentals haven’t changed. Protect the environment, detect early, respond before the process is impacted, and recover cleanly. The tools attackers have access to are evolving faster than we expected. Strong leadership, skilled teams, and disciplined execution of the basics is how you meet that.
Go forth and do good things, Don C. Weber
Image credit: Generated by Google Gemini on 2026-04-16. AI-generated image.
